Douglas Stebila
Obfuscated key exchange
Abstract
Censorship circumvention tools enable clients to access endpoints in a network despite the presence of a censor. Censors use a variety of techniques to identify content they wish to block, including filtering traffic patterns that are characteristic of proxy or circumvention protocols and actively probing potential proxy servers. Circumvention practitioners have developed fully encrypted protocols (FEPs), intended to have traffic that appears indistinguishable from random. A FEP is typically composed of a key exchange protocol to establish shared secret keys, and then a secure channel protocol to encrypt application data; both must avoid revealing to observers that an obfuscated protocol is in use.
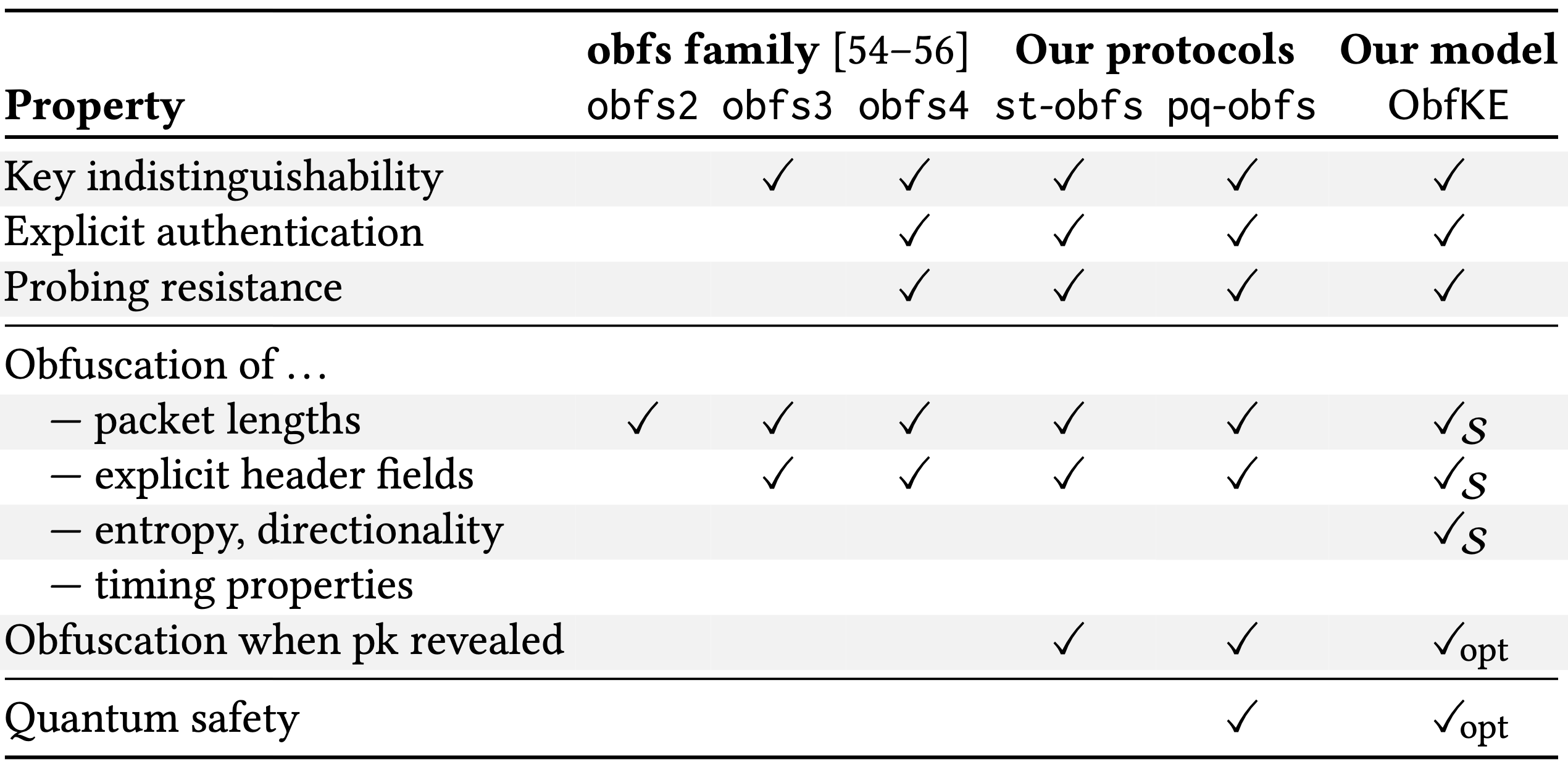
We formalize the notion of obfuscated key exchange, capturing the requirement that a key exchange protocol's traffic 'looks random' and that it resists active probing attacks, in addition to ensuring secure session keys and authentication. We show that the Tor network's obfs4 protocol satisfies this definition. We then show how to extend the obfs4 design to defend against stronger censorship attacks and present a quantum-safe obfuscated key exchange protocol. To instantiate our quantum-safe protocol using the ML-KEM (Kyber) standard, we present Kemeleon, a new mapping between ML-KEM public keys/ciphertexts and uniform byte strings.
Keywords: fully encrypted protocols, obfuscation, obfs4, ML-KEM, quantum-safe
Reference
Felix Günther, Douglas Stebila, Shannon Veitch. Obfuscated key exchange. In Engin Kirda, David Lie, editors, Proc. 31st ACM Conference on Computer and Communications Security (CCS) 2024, pp. 2385–2399. ACM, October 2024. © The authors.
Download
BibTeX
Funding
This research was supported by:- Natural Sciences and Engineering Research Council of Canada (NSERC) Discovery grant RGPIN-2022-03187
- NSERC Alliance grant ALLRP 578463-22